What’s Inside

Axionis Decision Intelligence System
Not a template. A system.
Cyber Threat Intelligence Triage System
Cut Daily Threat Monitoring to 15 Minutes With Audit-Ready Documentation
You’re the person responsible for cybersecurity at a 10–500 person company, but you don’t have a dedicated threat intelligence team — so every morning you’re manually scanning news feeds, vendor advisories, and alert emails with no consistent way to decide what actually matters to your environment. Generic security checklists and vendor blogs don’t account for your specific stack, your industry, or your actual asset exposure, so you either over-react to irrelevant threats or miss the ones that should have triggered action. This system gives you a weighted Threat Relevance Scoring Matrix cross-referenced against your own Asset-to-Threat Mapping Register, a tiered source index of 22 ranked intelligence feeds, and a weekly digest template that produces audit-ready documentation in 10 minutes. After 30 days of use, you’ll have a documented threat log that satisfies cyber insurance due diligence requirements and a repeatable 15-minute daily routine that replaces what used to take the better part of two hours.
Who This Is For
- IT managers at SMBs (10–200 employees) who handle security alongside 4 other job functions and have no dedicated threat analyst
- Security officers at professional services firms who need to demonstrate active threat monitoring to cyber insurers or compliance auditors
- MSP technicians managing security posture for multiple SMB clients who need a repeatable triage process they can run across accounts
- Operations managers at e-commerce or SaaS companies who own the security function by default and need a structured system before an incident forces one
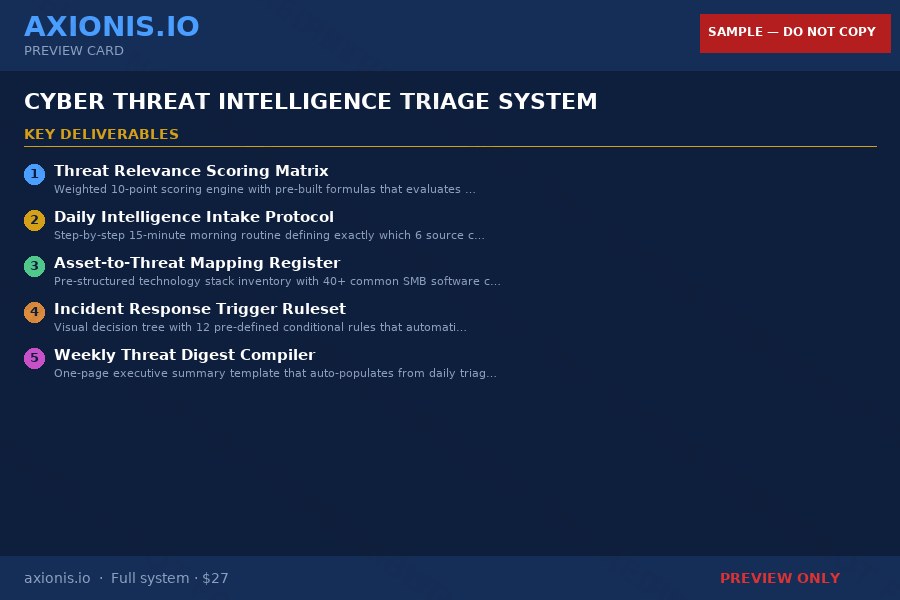
What’s Included
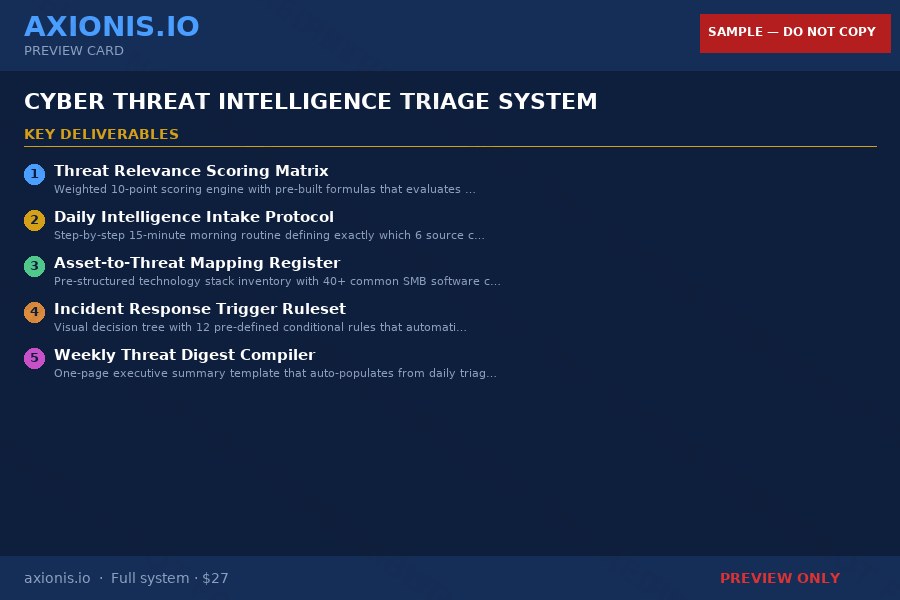
- Threat Relevance Scoring Matrix (Excel/Google Sheets) — pre-built 10-point weighted calculator across 5 dimensions with auto-color coding and 15 pre-scored real-world examples including Log4Shell and Heartbleed
- Daily Intelligence Intake Protocol (PDF + Notion Template) — 15-minute morning flowchart with 4 qualifying questions that route each alert to Tier-1 (act), Tier-2 (monitor), or Tier-3 (ignore)
- Asset-to-Threat Mapping Register (Excel/Google Sheets) — 40+ pre-populated SMB software categories with version tracking, EOL date alerts, and auto-lookup formulas that flag if a CVE affects your stack
- Incident Response Trigger Ruleset (PDF + Laminated Quick Reference Card) — 12 conditional rules with binary yes/no gates, 4 pre-written escalation email templates, and edge case handling for vendor-silent zero-days
- Weekly Threat Digest Compiler (PowerPoint/Google Slides) — one-page executive summary template with auto-populated risk trend chart, open items table, and a compliance statement paragraph for insurance and audit use
- Source Credibility Ranking Index (PDF) — 22 ranked intelligence sources across 3 tiers with RSS feed URLs, reliability scores, and Feedly setup instructions so you check the right 6 sources daily
- 30-Day Threat Pattern Log (Excel/Google Sheets) — rolling tracker with pre-built pivot tables, vendor blind spot analysis, attack vector trend charts, and a one-click audit-ready CSV export
How You’ll Use This
IT Manager, 80-person professional services firm
Preparing for cyber insurance renewal and needs to demonstrate 30 days of documented threat monitoring to the underwriter
→ Exports a complete audit-ready CSV from the 30-Day Threat Pattern Log in one click and submits it with the renewal application without reconstructing any records
MSP Technician managing 12 SMB clients
Needs a repeatable triage process to run across multiple client environments each morning without spending more than 20 minutes per account
→ Uses the Asset-to-Threat Mapping Register and Scoring Matrix as a per-client template, completing triage for each account in under 15 minutes with a documented score and action status
Operations Manager at a 60-person e-commerce company
Receives a CISA alert about an actively exploited vulnerability in a SaaS platform the company uses and has no process for deciding how urgently to act
→ Runs the threat through the Scoring Matrix, gets an 8.6 score triggering the IMMEDIATE ACTION flag, and sends the pre-written emergency escalation email to leadership within 20 minutes
Why It Matters
Cyber insurance premiums rose 28% in 2023 and underwriters are now requiring documented evidence of active threat monitoring — not just a firewall and antivirus. At the same time, CISA’s Known Exploited Vulnerabilities catalog added over 300 entries in the past 12 months, meaning the volume of credible threats hitting SMB environments is accelerating faster than any part-time security function can absorb without a structured filter.
IT managers without a triage system spend 60–90 minutes daily reading alerts they can’t prioritize, then produce nothing that satisfies an auditor or insurer when it matters. Those with a scoring system and documented log can demonstrate due diligence in under 10 minutes, respond to critical threats within a defined SLA, and walk into a cyber insurance renewal with 30 days of evidence already compiled — which directly affects both coverage eligibility and premium rates.
What You Get
- ✅ Daily threat monitoring drops from 90 minutes to 15 minutes using the tiered intake protocol and pre-ranked source index
- ✅ Audit-ready threat documentation is generated automatically from the 30-Day Log with one-click CSV export for insurance renewals
- ✅ Irrelevant alerts are filtered out in under 2 minutes using the 4-question decision tree that routes noise to Tier-3 before it wastes your time
- ✅ Critical threats trigger a defined response within 4 hours using the 12-rule Incident Response Trigger Ruleset — no judgment calls under pressure
- ✅ A complete weekly executive digest is compiled in 10 minutes using the pre-built PowerPoint template that pulls directly from your triage log
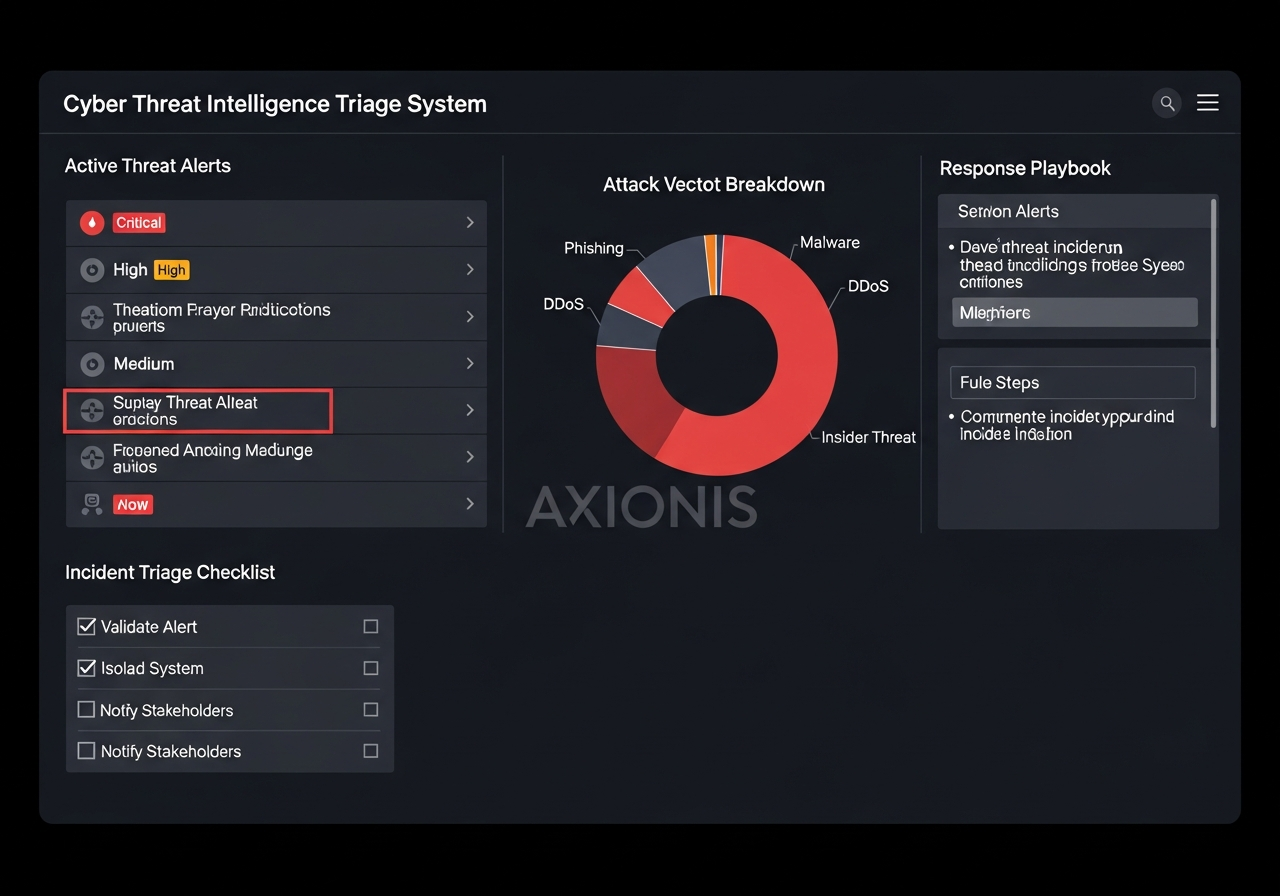
📊 System Preview
A three-panel Google Sheets view showing the Asset-to-Threat Mapping Register on the left with red-highlighted EOL assets, the Threat Relevance Scoring Matrix in the center with a CVE auto-scored at 8.4 triggering an IMMEDIATE ACTION flag in red, and the 30-Day Threat Pattern Log on the right displaying a line chart of daily scores with three overdue open items highlighted in orange.
🎁 Free Resource
The SMB Threat Triage Cheat Sheet: 6 Sources, 4 Questions, 15 Minutes
A one-page PDF that shows IT managers exactly which 6 sources to check daily and the 4 qualifying questions that separate actionable threats from noise — usable immediately without any paid tools
Download the Free Cheat Sheet →
Cyber insurers are now requiring documented threat monitoring — renewals without it are being denied.
👉 Download the Cyber Threat Triage System
One-time purchase · Instant download · No subscription
⚡ Complete the System
Pair this system with a Security Policy and Vendor Risk Assessment toolkit to cover the documentation gaps that threat monitoring alone doesn’t address — particularly third-party vendor exposure and employee access controls, which are the two areas cyber insurers scrutinize most after active monitoring.
📖 Related Intelligence Guides
👉 Best Ai News Today (2026 Guide)
👉 Best Openai News (2026 Guide)
👉 Best Openai News Today (2026 Guide)
👉 Technology News Today That Work in 2026: Tools, Methods, and Starting Points
Filed under: Business Tools
⚡ Axionis
Decision Intelligence System
Support: support@axionis.io
Digital download · Instant access · One-time purchase
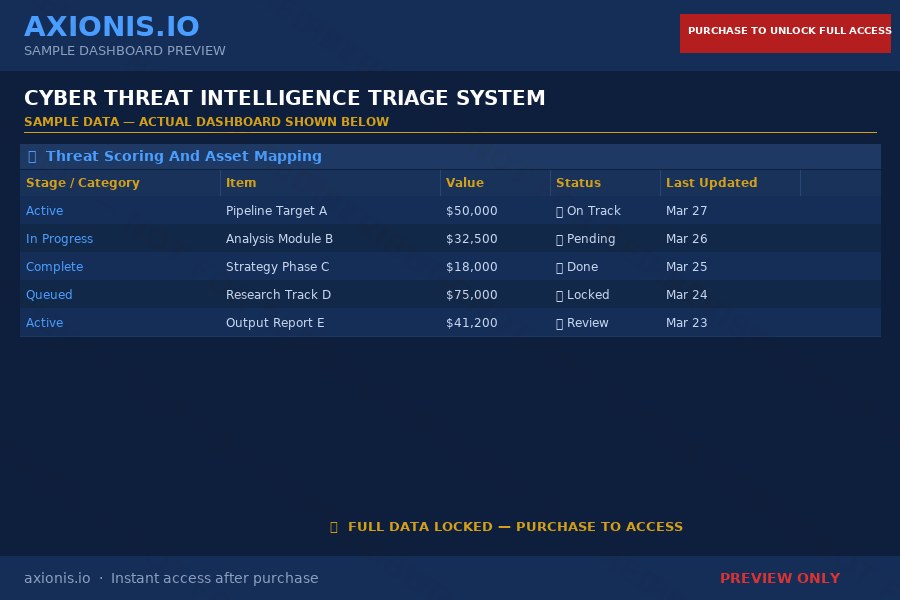
These are watermarked preview samples. Full, clean versions are delivered instantly after purchase.
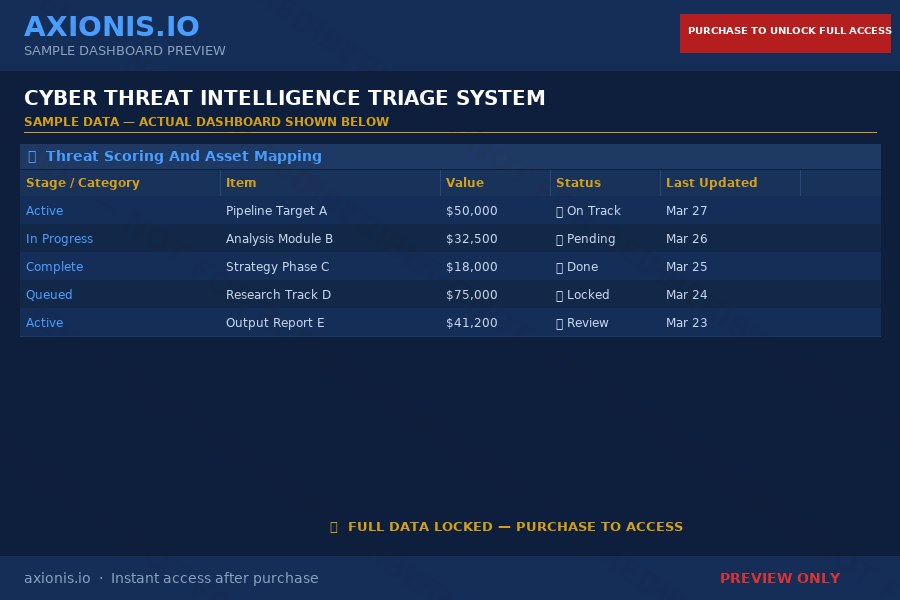
These are watermarked preview samples. Full, clean versions delivered instantly after purchase.
